Requirements
Linux
KDE
A Windows server to connect to.
Step 1: Install required software
yum install kde-plasma-networkmanagement-pptp NetworkManager-pptp
Step 2: Configure the network
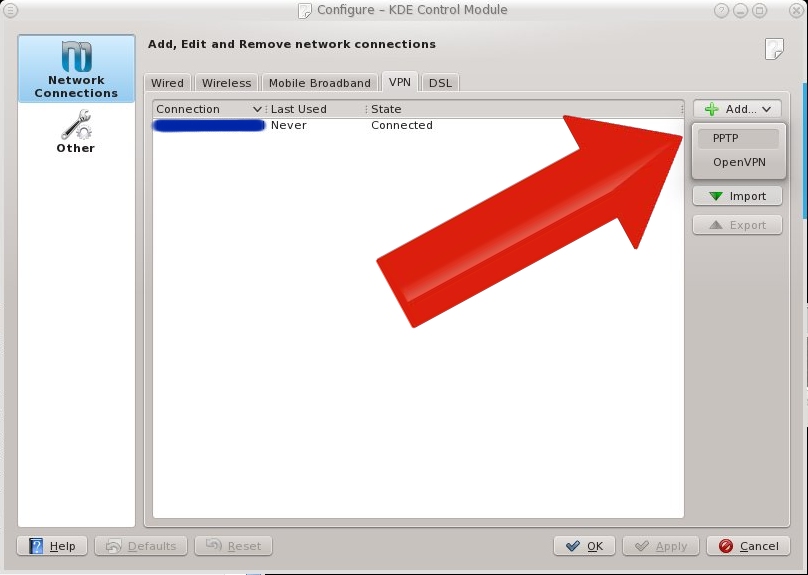
In the KDE Network Manager plasma module, go to the tab VPN, click add and choose PPTP.
Enter and connection name you like. In the field "gateway" type the hostname or IP number of the Windows server you're connecting to. Under Login, Password and NT Domain, fill in your authentication data. Then click advanced.
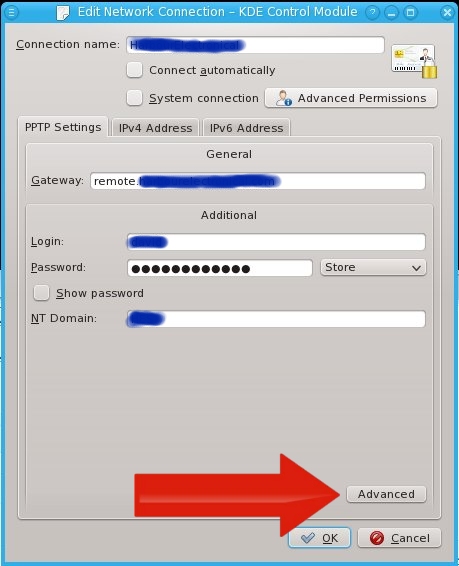
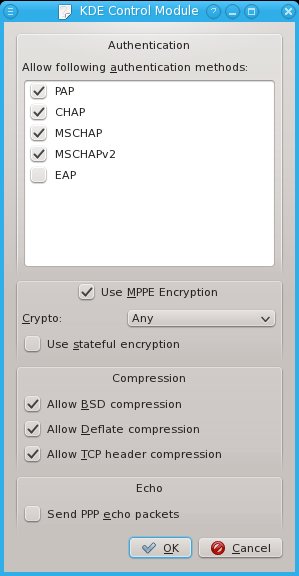
In the advanced window, disable EAP and enable MPPE. Then click OK.
Go to the tab IPv4. Under method, I chose Automatic (VPN). But Automatic (VPN) addresses only is also a nice option: it sets the IPs but no DNS settings.
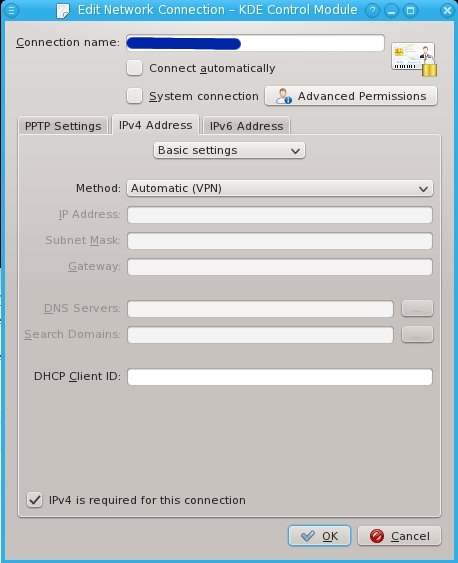
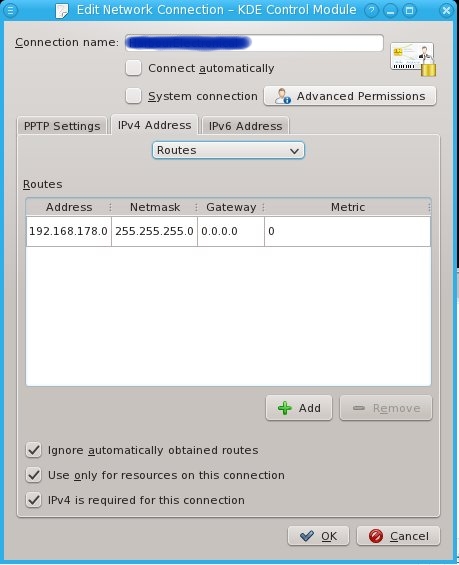
Go to the routes sub-tab. Switch on Ignore automatically obtained routes and Use only for resources on this connection to make sure the connection doesn't steal your traffic. Then I entered a manual route: 192.168.178.0/255.255.255.0 to gateway 0.0.0.0 (it is a ppp device after all).
You may want to configure IPv6 as well, but I don't at this moment, so I'm not documenting this.
Step 3: Connect
Click on the icon in the tray and connect.
Ubuntu/Debian
I'm running RedHat-based software on all of my machines. Above information may be useful for Ubuntu/Debian users, but it's not tested and I'm not supporting it.Servers: RedHat Enterprise Linux/CentOS is more suitable for servers, as there's a lot of professional level support available. I think that's important, because if I say, get a car accident, I want the servers to be managable by another professional.
Desktops/Laptops: RPM packages are pretty exchangable between RedHat-based platforms. That's a good reason to run Fedora on the desktop.

