Step 1. Install ntp and synchronize clocks
We'll be using winbind, kerberos and ntlm to authenticate the user. This requires the clocks of the AD server and the proxy server to be synchronized.
yum -y install ntp
sed -i "s/^server /#server /g" /etc/ntp.conf
echo "server YOURSERVERNAME" >> /etc/ntp.conf
ntpdate YOURSERVERNAME #synchronize right now
service ntpd start #and keep in sync
chkconfig ntpd on #after reboot as wellStep 2. Update system and install required software
yum update
yum install mc vim httpd php svn httpd-devel make autoconf gcc ntp krb5-workstation \
samba-common authconfig samba-winbind
Step 3. Connect to active directory
Please note that MYCOMPANY.local and mycompany.local may be different domains due to the upper/lowercase.
ADSERVER=sbs.MYCOMPANY.local
DOMAIN=MYCOMPANY.local
WORKGROUP=MYCOMPANY
authconfig --enableshadow --enablemd5 --passalgo=md5 --krb5kdc=$ADSERVER \
--krb5realm=$DOMAIN --smbservers=$ADSERVER --smbworkgroup=$WORKGROUP \
--enablewinbind --enablewinbindauth --smbsecurity=ads --smbrealm=$DOMAIN \
--smbidmapuid="16777216-33554431" --smbidmapgid="16777216-33554431" --winbindseparator="+" \
--winbindtemplateshell="/bin/false" --enablewinbindusedefaultdomain --disablewinbindoffline \
--winbindjoin=Administrator --disablewins --disablecache --enablelocauthorize --updateall
service winbind start ; chkconfig winbind on
setsebool -P allow_httpd_mod_auth_ntlm_winbind on
Now check your winbind connection using the following commands:
wbinfo -u
wbinfo -g
The socket /var/lib/samba/winbindd_privileged/pipe should be writable by the webserver. To allow that access, I add user apache to the group wbpriv: usermod -G wbpriv apache
Step 4. Download and compile mod_auth_ntlm_winbind
svn co svn://svnanon.samba.org/lorikeet/trunk/mod_auth_ntlm_winbind mod_auth_ntlm_winbind
cd mod_auth_ntlm_winbind/
autoconf
./configure
apxs -DAPACHE2 -c -i mod_auth_ntlm_winbind.c
Step 5. Configure it
In /etc/httpd/conf.d/mod_auth_ntlm_winbind.conf I put the following configuration
LoadModule auth_ntlm_winbind_module /usr/lib64/httpd/modules/mod_auth_ntlm_winbind.so
Options ExecCGI
AllowOverride None
Order allow,deny
Allow from all
AuthName "NTLM Authentication"
AuthType NTLM
Require valid-user
NTLMAuth on
NTLMAuthHelper "/usr/bin/ntlm_auth --helper-protocol=squid-2.5-ntlmssp"
NTLMBasicAuthoritative on
In /etc/httpd/conf/httpd.conf, change KeepAlive Off to KeepAlive On. Preferably, also set MaxKeepAliveRequests and KeepAliveTimeout to a high value. On my intranet server, they're set to 1000 requests and 600 seconds.:w
Step 6. Change your firewall to enable incoming HTTP
iptables -I INPUT -p tcp --dport 80 -j ACCEPT
service iptables save
Step 7. Go!
Run service httpd restart, make httpd start on reboot using chkconfig httpd on and test your configuration.
© GeekLabInfo Install mod_auth_ntlm_winbind on CentOS 6.0 is a post from GeekLab.info. You are free to copy materials from GeekLab.info, but you are required to link back to https://www.geeklab.info
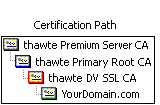 Normal "single root" certs are only certified by one single parent which is recognised by clients immediately. Chained certs on the other side are signed by a parent which itself is signed by another parent. This effectively makes your cert a "grandchild" of the CA root. In the image attached you'll see a cert that is chained by two intermediate certs.
Normal "single root" certs are only certified by one single parent which is recognised by clients immediately. Chained certs on the other side are signed by a parent which itself is signed by another parent. This effectively makes your cert a "grandchild" of the CA root. In the image attached you'll see a cert that is chained by two intermediate certs.
 (8 votes, average: 3.88 out of 5)
(8 votes, average: 3.88 out of 5)